Deploying KeyAccess with JAMF to Mojave

If you manage Macs, it’s a good guess that you do so using JAMF. Most likely then, you’ve also deployed KeyAccess using JAMF Pro. There’s a new twist with KeyAccess 7.5 and Mojave, but it can be handled easy by following the steps here.
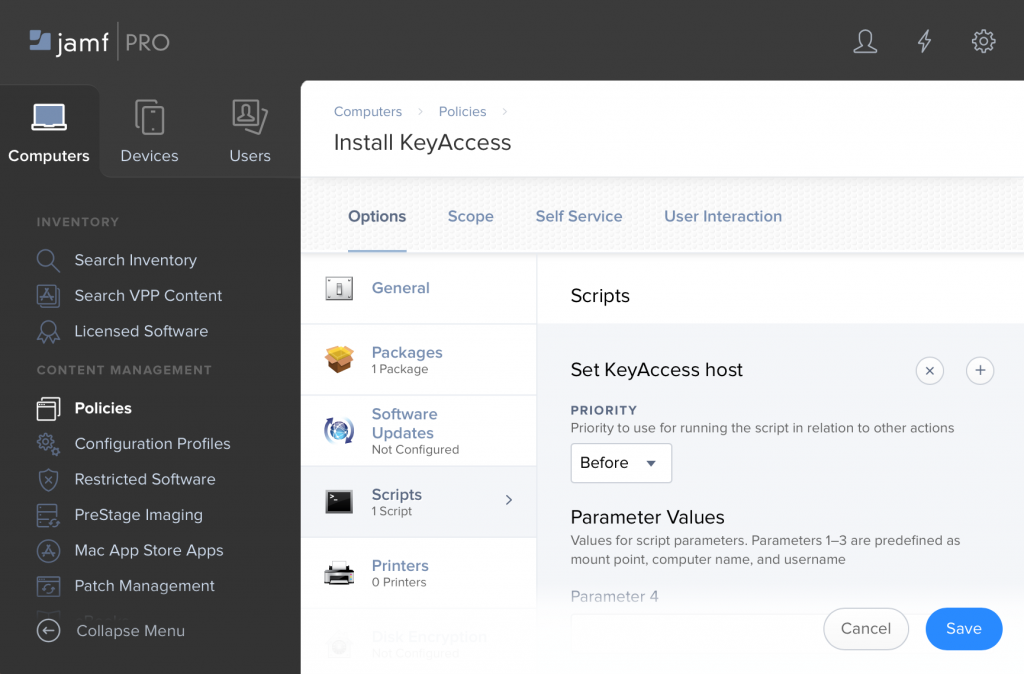
First let’s look at a simple deployment policy for KeyAccess in JAMF. It is very simple – we have uploaded a KeyAccess installer (K2Client.pkg) for the version we want to deploy. Choose whatever Triggers you’d like to use. If you will use the Self Updating featuring for KeyAccess, you might configure JAMF to install just once. If instead you’ll manage new versions of KeyAccess entirely in JAMF you might choose differently.
As with any JAMF policy, you will choose a scope. The only other step is to create a script in JAMF that sets the KeyServer address. The contents of the script is just:
defaults write /Library/Preferences/com.sassafras.KeyAccess host keyserver.myorg.org
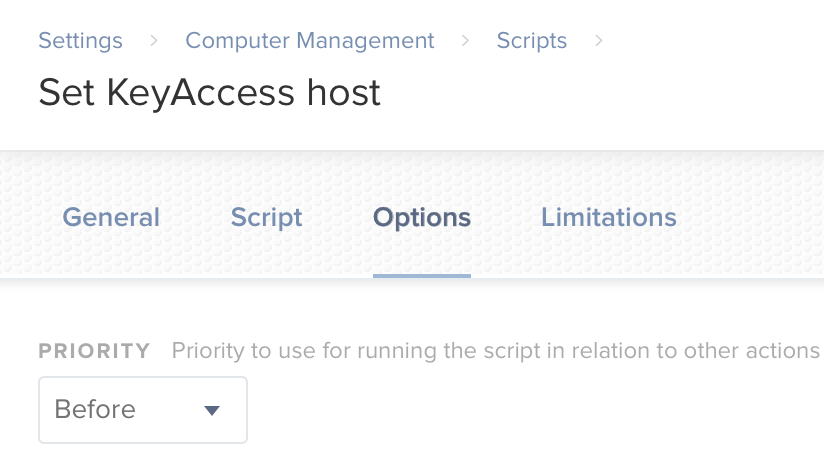
and the script uses the default priority of “before”, so that the host will already be set the first time that KeyAccess starts. Generally then this is all that is needed for a basic install. The install will happen silently, and we’ve specified the KeyServer address which is the only important configuration or customization.
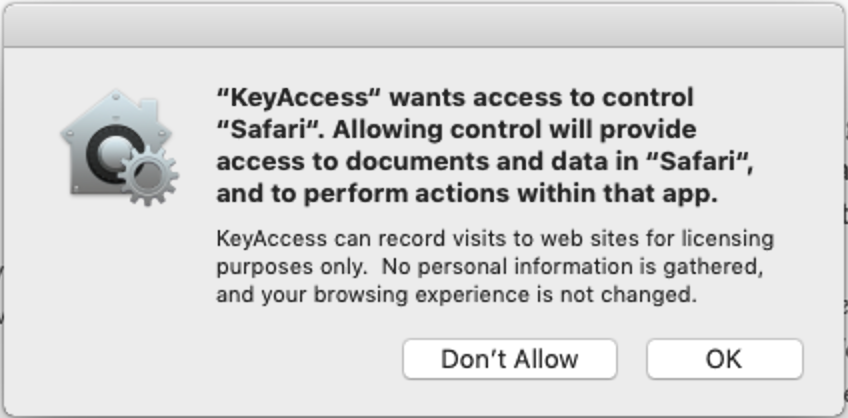
So far this is all very simple. Then in version 7.5 of KeyAccess, we added the ability to Track URLs. Then with the release of Mojave, Apple decided that this sort of thing needed an extra layer of protection – so with KeyAccess on Mojave, each user would see a dialog like this one the first time they ran any browser:
This type of dialog is not unique to KeyAccess – you’re probably cursing compatibility in Mojave unlike in any other recent release. Here are the two quick ways to remove these dialogs on Mojave.
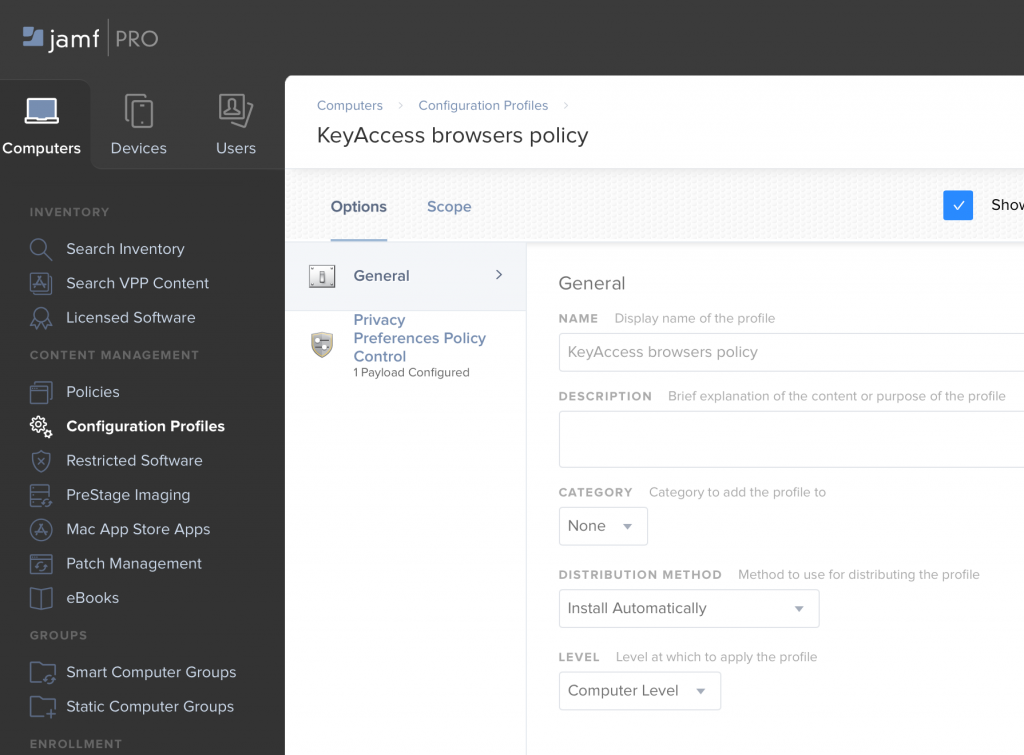
First, you can set up a Configuration Policy in JAMF to deploy a Privacy Preferences Policy Control which specifies that KeyAccess should be able to communicate with each of the major browsers. You can download a PPPC file here:
All you have to do is upload it when creating your Configuration Profile. Most likely you’ll apply it at the Computer level.
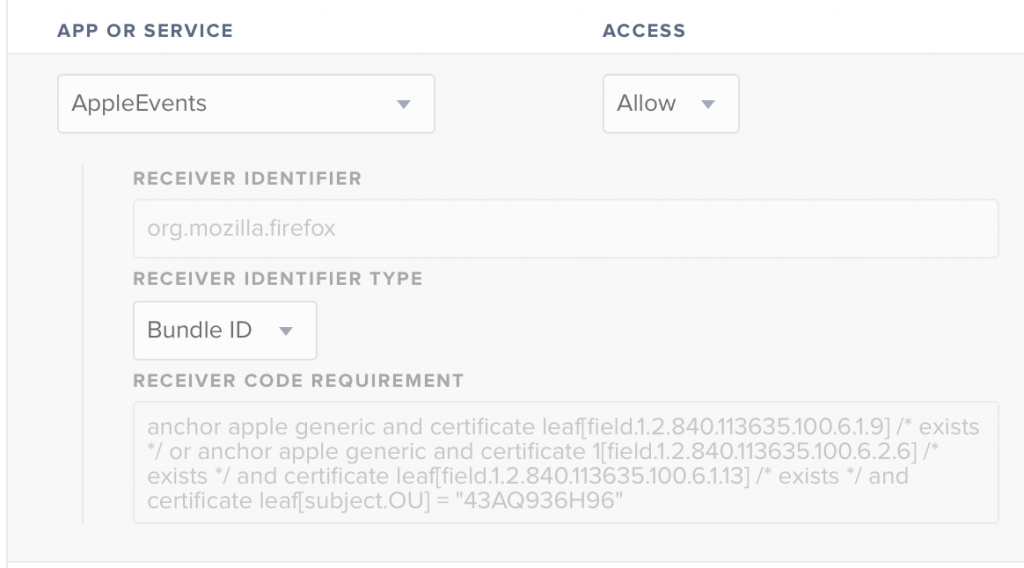
After uploading, if you examine it you’ll see that it just specifies that KeyAccess should be allowed to send AppleEvents to each major browser, e.g.:
Second, as an alternative, you might decide that you don’t need to track any URLs and would like to disable this functionality entirely on the client. To do so, modify the script that sets the KeyServer address, to add a second defaults write:
defaults write /Library/Preferences/com.sassafras.KeyAccess host keyserver.myorg.org
sudo defaults write /Library/Preferences/com.sassafras.KeyAccess nourl 1
However, we recommend leaving URL tracking on, and thinking about how you might use it. It is likely that you are paying for cloud services and it would be useful to know who is accessing those services and how frequently. You might also configure tracking for any websites created and maintained by your internal IT team, to determine if there is value in spending development resources on those pages.
As always, don’t hesitate to request support if any of this is unclear or you need any assistance.
Author: Michael Maddalena
Having tested and supported KeyServer since as far back as version 3.2, Michael has been working with some long-term customers for decades now, but is always happy to help anyone (Old Hands, New or Recent customers, or Prospects) understand and get the most out of our software. He also handles any questions related to bees or goats.
Site Search
Documentation Search
Categories

Social
Subscribe
| Thank you for Signing Up |


Neil Clarke Drew UniversityWe’re very pleased with our choice of KeyServer. We’ve expanded our use and rely on it heavily. We couldn’t offer half of what we do without it and most people don’t know it’s there. We’ve also been able to establish licensing contracts a lot more smoothly with this in place. It’s a well-respected product.
Chuck White US Defense Contractor (company name withheld)I’ve worked with your product now for many years, and I have never worked with a server or technology which is as simple to use and just runs year after year after year. The only thing that changes is the increased capabilities. K2’s reliability, cross platform support, and incredible functionality amaze me. You all are to be congratulated.