Convince Your Boss
Interested in KeyServer but need to convince others to make the investment?
If your boss understands that better management means better financial efficacy, but is still on the fence about making the investment in good IT asset management, you’re in the right place. We discuss below how some common objections can be countered by a closer examination and by taking a look at the experience of other IT managers.
“Not in the budget”
A common objection goes something like this: “We’re already spending too much on software, and we just can’t spend more right now.” In response to this objection, we often point out that after 30 years in the market, we have thousands of enthusiastic customers scattered around the globe precisely because of KeyServer’s time-tested ability to help our users control costs and save money. We know that the initial investment for most KeyServers is recouped within the first year through improved efficiency and reduced costs because we’ve seen it happen again and again. When customers see true usage data, they react in disbelief, then quickly start to understand how that data can be leveraged.
We offer both subscription and perpetual pricing and we can work with you to set up a large scale proof of concept that specifically focuses on your goals with no financial risk.
“Software Asset Management is obsolete”
It’s true that publisher-enforced license management and subscription-based metrics have reduced the need for active concurrent use license management—but KeyServer does a lot more than simply make sure you don’t use more copies of a product than you’re entitled to. From automatic product discovery and normalization to detailed hardware and software usage gathering, KeyServer helps you understand exactly how your IT assets are being used, leading to a much more efficient allocation of resources. Why purchase new what can be re-harvested from somewhere else where it’s not being used? Why purchase (and support) a site license for software that is rarely or never used?
“We already use SCCM”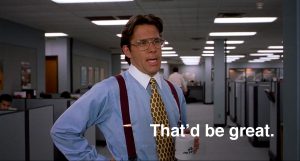
As a software deployment and network configuration tool, SCCM is irreplaceable. But as an audit and usage reporting tool, inaccurate, missing, and fragmented data severely limit its usefulness. KeyServer is different. By maintaining constant awareness of what software is installed and used on client machines, automatically normalizing raw data into meaningful insights, KeyServer is able to provide a truly accurate snapshot of usage across any time span and any set of computers or users you choose. Also, at many sites, KeyServer acts as a check on other technologies such as SCCM and Active Directory – in theory, these technologies know all there is to know about their clients, but in practice there are often discrepancies that can only be noticed from a different point of view.
“SAM tools are difficult to learn and implement”
While the fine print in your licensing contracts may be complex and difficult to understand, KeyServer is not. KeyServer is, however, highly flexible, with a robust feature set and fine-grained controls. This flexibility is sometimes misconstrued as complexity, but KeyServer implementation can actually be reduced to 3 or 4 simple stages:
- Deploy — Install KeyServer and deploy client agent to target computers. The database is integrated and both the server process and client app are lightweight, reliable, scalable, with support for: Windows, Mac, Linux, and Solaris.
- Discover — Hardware details and installed software are automatically discovered and normalized. 20 minutes after the client is deployed you’ll have access to a wealth of information about the hardware and software on your network.
- Decide — Automatically group computers into divisions by name prefix, OU, or IP address range, and then create policies to track usage for the software and web-based products that matter. When starting with policies to simply observe usage, you can complete the initial implementation and configuration between cups of coffee. Return after a few weeks of usage data has been compiled to fine-tune the policies by focussing some on specific groups of computers etc.
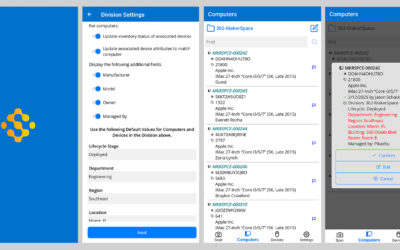
- Design — In campus environments, an optional step is to draw and place computers in various computer lab, library, or tech centers, and then publish computer availability, OS details, and software availability information as a web page for end user access on a smart phone.
Conclusion
If your organization is struggling to restrain costs on IT assets, the idea of spending more to spend less may sound counterintuitive and risky. If overspending is already a problem, who wants to put their budget on the line for a solution that might not work? The problem is that, while everyone knows how much money they spend versus how much they have to spend, most organizations still have no idea whether all that money is being spent wisely—because they simply don’t have enough data.
It’s like hiring a star quarterback and not keeping track of his stats—how do you know if he’s worth the money? Likewise, how do you know how many copies of Microsoft Office, Adobe Creative Cloud, or SPSS to buy next year, and where to deploy them, if you’re not keeping track of how much of this year’s supply is actually being used. With an effective Software Asset Management program, you can run reports that compile this information, across any set of computers, users, and time periods, in just a matter of seconds—and that’s just the beginning.
Author: Jason Schackai
Training and implementation specialist by day, user experience designer by night, Jason helps users learn the ropes of Sassafras, while mining their difficulties for ways to improve the product. As his father once told him: “Join me, and I will complete your training. With our combined strength, we can end this destructive conflict and bring order to the galaxy!”
Site Search
Documentation Search
Categories

Social
Subscribe
| Thank you for Signing Up |


Steve Burling University of MichiganOnce again, you’ve anticipated my needs. Thanks!
Rurik Spence Colby CollegeYour service has always been spectacular. And K2 is a rock in the midst of chaos. Keyserver has become more popular this year than I ever imagined. A tribute to its reliability and ease of use.