Although your KeyServer contains a wealth of information about the computers on your network (and the software installed on them), some read/write actions can only be performed one-at-a-time in the […]
Currently browsing: Tech Blog
Sassafras Printer Management Integration
Note: This blog is outdated. Please see https://www.sassafras.com/hrl/7.7/general_settings.html#printers for current documentation on using this feature in new versions of Sassafras and PaperCut. Have you ever considered leveraging the data from […]
Short-Burst Training Tutorials
Rather than sit through our comprehensive “Fundamentals” training course, many new KeyServer admins would prefer an indexed list of topic specific, “short burst” videos that cover all the highlights of […]
Deploying KeyAccess with JAMF to Mojave
If you manage Macs, it’s a good guess that you do so using JAMF. Most likely then, you’ve also deployed KeyAccess using JAMF Pro. There’s a new twist with KeyAccess […]
KeyServer integration with Modo Campus
KeyServer Maps are an incredibly powerful way to allow students to view resource availability – both hardware and software. The simplest way to provide this data is a direct link […]
How to Track URLs in Sassafras KeyServer
URL tracking is a long-requested feature that has now been implemented in KeyServer 7.5, so we wanted to provide a quick tutorial on how to use it. Check out […]
Sassafras Software Launches a Major New Release of Award-Winning KeyServer Application
On 7/5, Sassafras released the hotly anticipated 7.5 version of KeyServer, our award-winning Hardware and Software Asset and Management tool. Voted #1 in Customer Satisfaction by the readers of The […]
KeyServer Fundamentals Video Training Course
We’ve heard it a thousand times: “We don’t need SAM anymore because Adobe and Microsoft went to the cloud and we just buy site licenses for everything now.” In other words: “We […]
Choosing a Computer ID Type
With any system that maintains a database of computers, a critical question is how each record is uniquely identified. For many organizations, identifying computers simply by Computer Name is sufficient […]
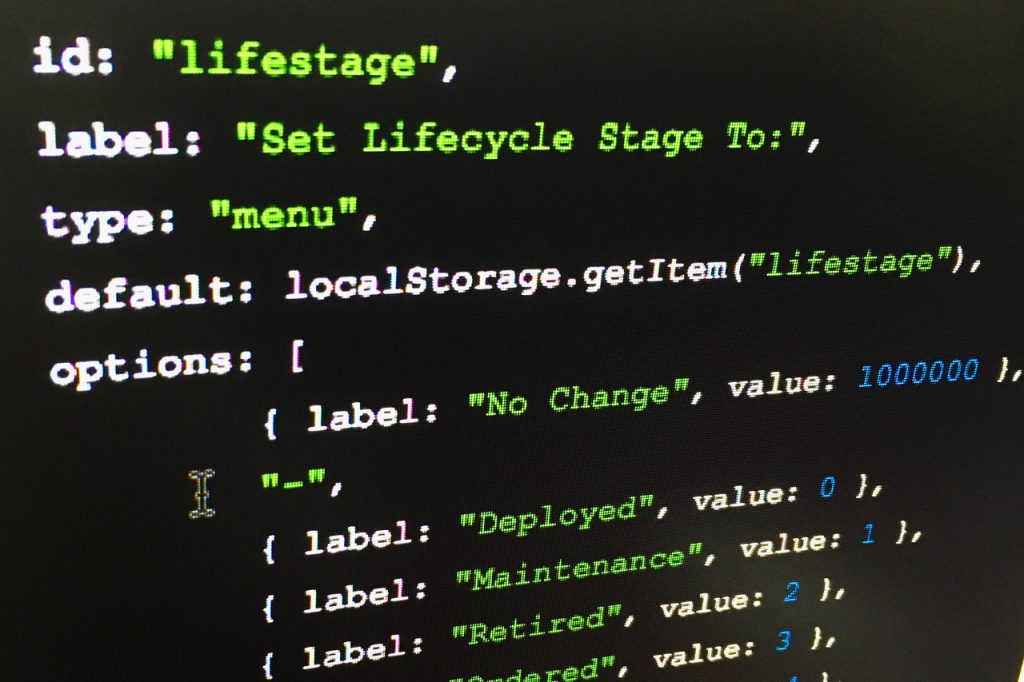
Tracking Departments During Client Deployment
During installation of the K2 client, a “Department” field can be placed on the client. This value is then sent from KeyAccess to KeyServer, and can be used in a […]
Site Search
Documentation Search
Categories

Social
Subscribe
| Thank you for Signing Up |