Contact tracing in computer labs
Just in Case
This year has certainly been “unique” – many of us are looking forward to saying goodbye to 2020. One common element has been the need to quickly adapt to brand new situations. Scrambling to find a solution is never fun, so at Sassafras we have done our best to look ahead, anticipate needs, and put features in place before they are needed. Earlier this spring as coronavirus began to threaten to close universities, we started to build functionality around providing remote access to computers, before it was broadly needed.
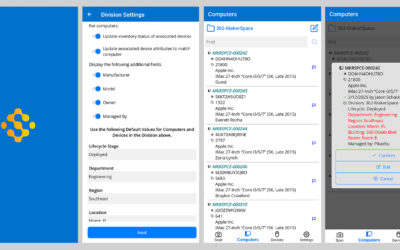
Today, we’re introducing a feature we hope you will never need to use. This feature is an “extra” for contact tracing based on computer logins. If you have public labs, and if you’ve reopened them for physical access, you’ve certainly thought about sanitation protocols. But what if someone tests positive for COVID-19, and they’ve been in a lab? Can we leverage login events to do contact tracing – potentially identifying contacts that might be hard to narrow down in other ways? Well, this is exactly what we have added to Sassafras LabSight and AllSight.
What it does
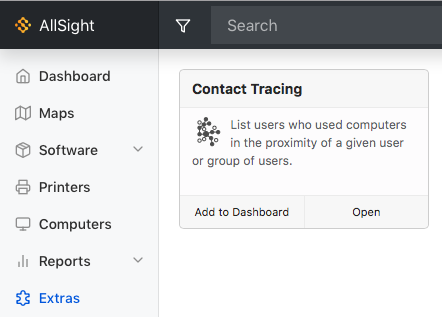
Once installed (see easy steps below), it will appear in the “Extras” navigation item (be sure that your KeyServer process has been upgraded to 7.7.0.2). The first step is to specify a few parameters. First and most importantly, choose one or more user names to trace. Next, choose which map to use – this is important because it will indicate which computers are in the same room. If you only have one map, or you don’t change this, the Default Map should be based on computer divisions. If you have for example a tag based map you might use that instead. Next, choose the date range to consider. CDC guidelines suggest contact tracing starting 2 days before symptoms start or a positive test result. Finally, you can specify a threshold both “before” and “after” – meaning before and after we know the particular user logged in. The after threshold can be used since droplets may remain suspended in the air even after the person has left the room. The before threshold is provided in case people enter the room but do not immediately login to a computer.
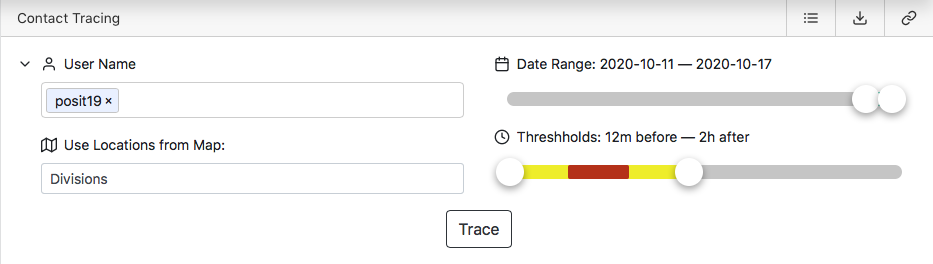
Once you click “Trace”, data will be gathered and analyzed. Assuming the user has logged in to a computer in a location with other users, you should see results like this:
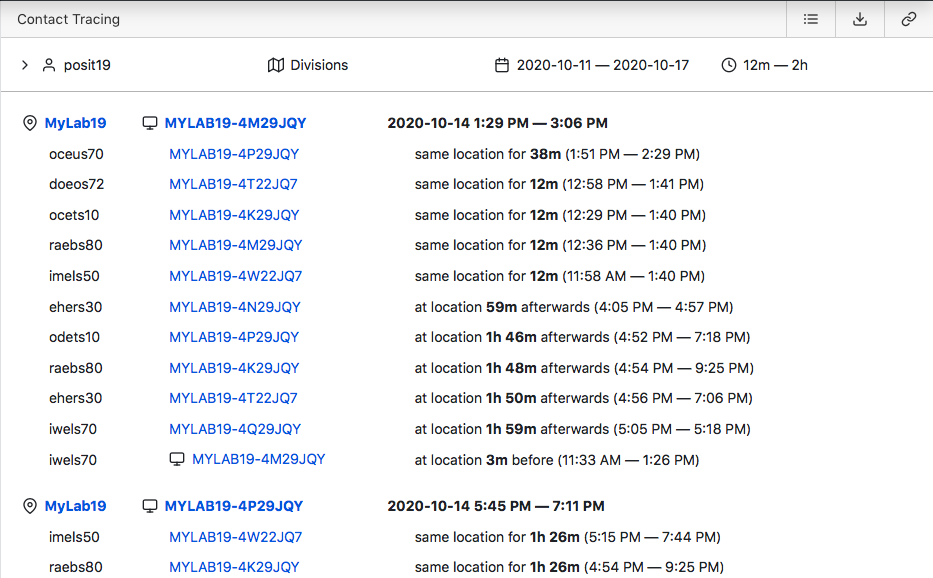
In this view, contacts have been organized by each login initiated by the person being traced, and prioritized by the degree of contact – i.e. someone who was in the room for a longer time will be ranked first.
Alternatively you can click the icon at the top right to switch to a “flat” view which simply shows all the people who had some contact.
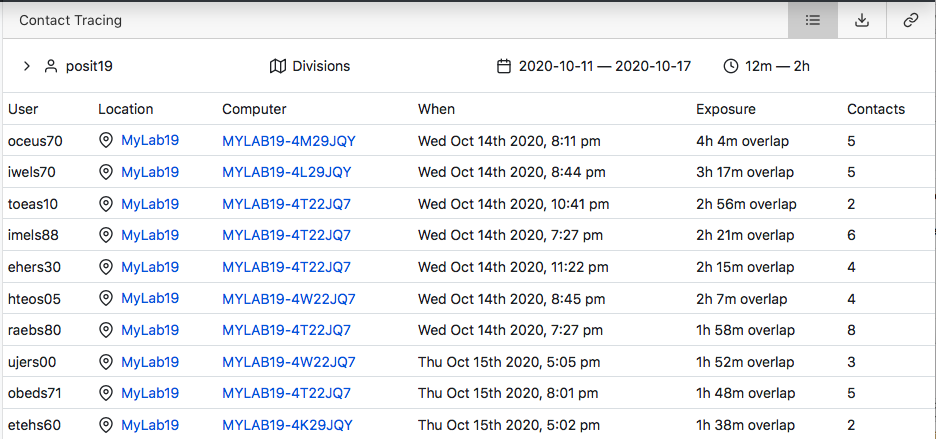
In either view, you can download a csv file containing the data.
Contact can be one of essentially three types:
– In the room at the same time
– In the room soon before or after
– On the same computer after the traced individual used it
Note that in recent releases (KeyAccess 7.6.0.9, KeyServer 7.7.0.1), remote connections can be recognized and will be recorded in usage data – these logins will be removed from the results displayed for contact tracing, since no physical contact was made.
Installing
- Make sure that the KeyServer component has been upgraded to 7.7.0.2
- Download the zip here
- Login to the web UI and navigate to “Settings” on the left, then “Extras” in the secondary navigation
- Drag the downloaded zip onto the text at the bottom of the page (“Drag an app archive here to add it to the list”)
- Navigate to Extras and you should see Contact Tracing
Our Hope…
That’s it, in a nutshell. We hope you never need to use it. But if you do, it’s ready for you.
Author: Julian Devlin
Site Search
Documentation Search
Categories

Social
Subscribe
| Thank you for Signing Up |


Mary Mielke University of Wisconsin, Stevens Point…there can be a distance of lightyears in the value different companies place on providing support, with scattered few companies offering a level of customer and product support which is both comprehensive and well-executed… Thank you for the exemplary support Sassafras provides.
Lance Gallup (company name withheld by request)I work with the tech support people at many companies as part of my duties here. I wanted to let you know that in my experience, this kind of service is far above the norm.